How to Spot a Phishing Email: Protecting You or your Business from Cyber Threats
How to Spot a Phishing Email: Protecting You or your Business from Cyber Threats
This is a subtitle for your new post
What is a Phishing Email?
A phishing email is a fraudulent email designed to deceive recipients into taking a specific action, such as clicking on a malicious link, providing sensitive information like passwords or credit card numbers, or downloading malware onto their computer. These emails often seem to come from trusted sources like banks, government agencies, or well-known companies. Still, they are sent by cybercriminals with malicious intent.
How to Detect a Phishing Email:
- Check the Sender's Email Address: One of the simplest ways to spot a phishing email is to check the sender's email address. Be wary of emails from unfamiliar or suspicious email addresses, especially if they claim to be from a trusted organization.
- Look for Spelling and Grammar Errors: Phishing emails often contain spelling and grammar errors or awkward phrasing. Legitimate organizations typically have professional communication standards and would not send out emails riddled with mistakes.
- Verify Links Before Clicking: Hover your mouse over any links in the email to see the actual URL. If the link looks suspicious or doesn't match the purported destination, it's likely a phishing attempt. Avoid clicking on any links in the email.
- Watch Out for Urgency or Threats: Phishing emails often use urgent language or threats to pressure recipients into taking immediate action, such as claiming that your account will be suspended unless you provide personal information. Be skeptical of any email that tries to rush you into making a decision.
- Check for Unusual Requests: Be cautious of any email that asks you to provide sensitive information, such as passwords, credit card numbers, or social security numbers, especially if the request seems unusual or unexpected.
- Look for Generic Greetings: Phishing emails often use generic greetings like "Dear Customer" instead of addressing you by name. Legitimate organizations typically personalize their communications with customers.
- Still in doubt? Give us a call at 941-493-5126
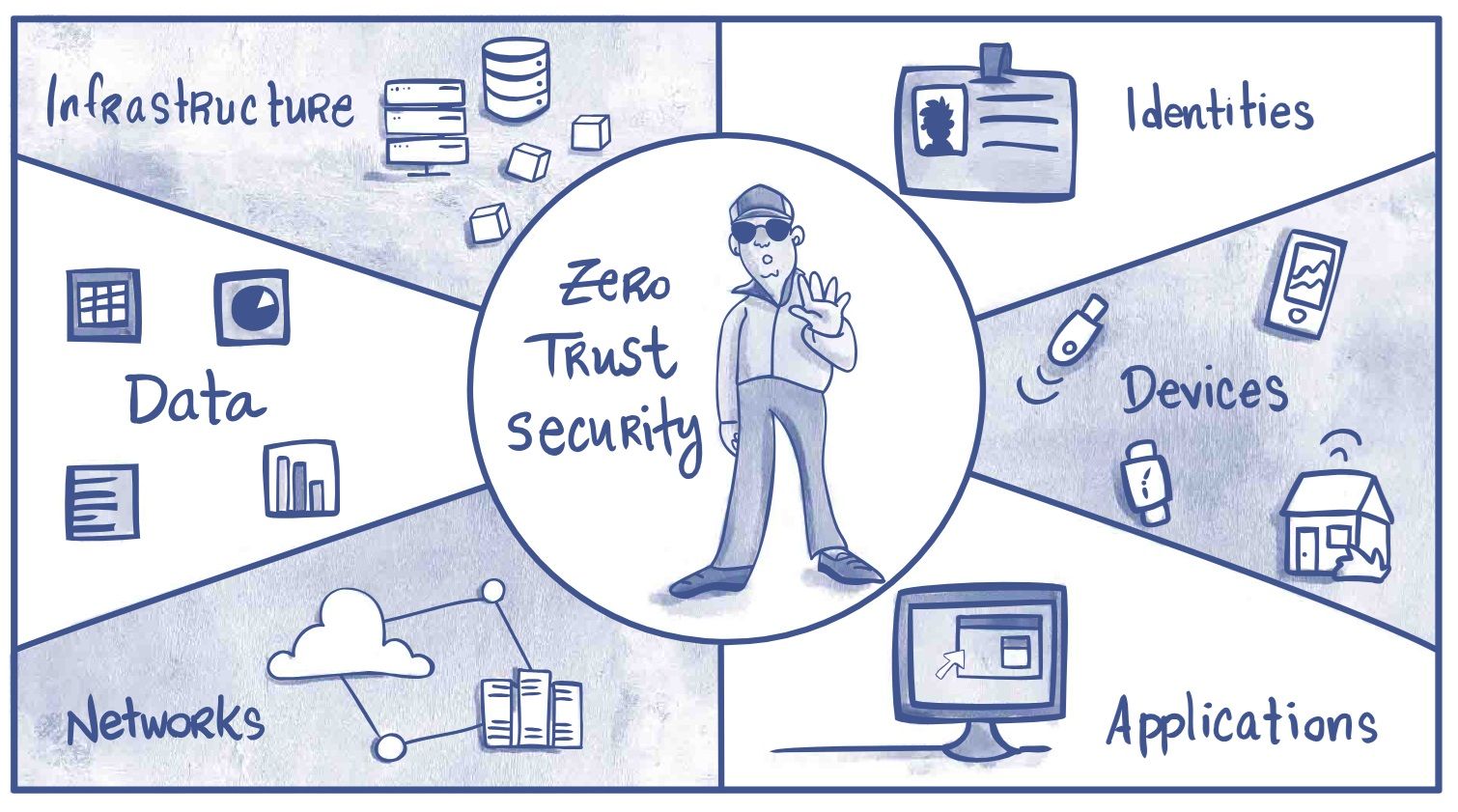
How MSP Solutions Can Help:
Managed Service Providers (MSPs) are crucial in helping businesses detect and prevent phishing attacks. Here's how:
- Email Security Solutions.
- Employee Training and Awareness.
- Regular Security Assessments.
- 24/7 Monitoring and Incident Response.
In conclusion, phishing emails pose a significant threat to businesses of all sizes. Still, with the right knowledge and tools, you can protect your business from falling victim to these attacks. By understanding how to detect phishing emails and partnering with an MSP that offers comprehensive cybersecurity solutions, you can safeguard your business from cyber threats and keep your data safe and secure. Click here for a FREE Assesment.
Stay vigilant, stay safe!